Claude Code Security Ultimate Guide - How AI Detects Software Zero-Day Vulnerabilities | Anthropic Security Innovation (2026)
📸 Claude Code Security by Anthropic aims to detect and patch ...
What Is Claude Code Security? — AI That Finds Code Vulnerabilities Autonomously
On February 20, 2026, Anthropic unveiled Claude Code Security, a groundbreaking tool with the potential to reshape software security. As Anthropic’s first dedicated AI product for cybersecurity, it goes far beyond traditional static analysis tools that merely scan for code patterns. Instead, Claude Code Security explores entire codebases the way a skilled security researcher would—intelligently, contextually, and holistically.
In an exclusive interview with Fortune, Frontier Red Team lead Logan Graham explained: "This is the next step in our evolution as a company committed to strengthening cyber defenses. It will act as a force multiplier, dramatically boosting the capabilities of security teams."
📸 Claude Code: What It Is, How It's Different, and Why Non ...
Why Software Security Is in Crisis
Unpatched software bugs remain the leading cause of data breaches, service outages, and regulatory penalties—even in large enterprises. The core issue? Scale. The average enterprise environment spans millions of lines of code across dozens of interconnected services, each with complex dependencies.
Traditional Static Application Security Testing (SAST) tools rely on detecting known vulnerability patterns. While effective for known issues, they fail to detect new, previously unknown vulnerabilities (Zero-Days) that emerge from interactions between components. These are precisely the blind spots attackers exploit most frequently.

📸 Anthropic rolls out embedded security scanning for Claude ...
How Claude Code Security Works: Core Mechanism
📸 What comes next, if Claude Code is as good as people say.
1. Full Codebase Contextual Analysis
Unlike conventional tools, Claude Code Security analyzes the entire codebase as a single contextual unit—not in isolated files or functions. It traces how data flows between modules and tracks where inputs propagate. This enables detection of cross-component vulnerabilities that traditional tools routinely miss.
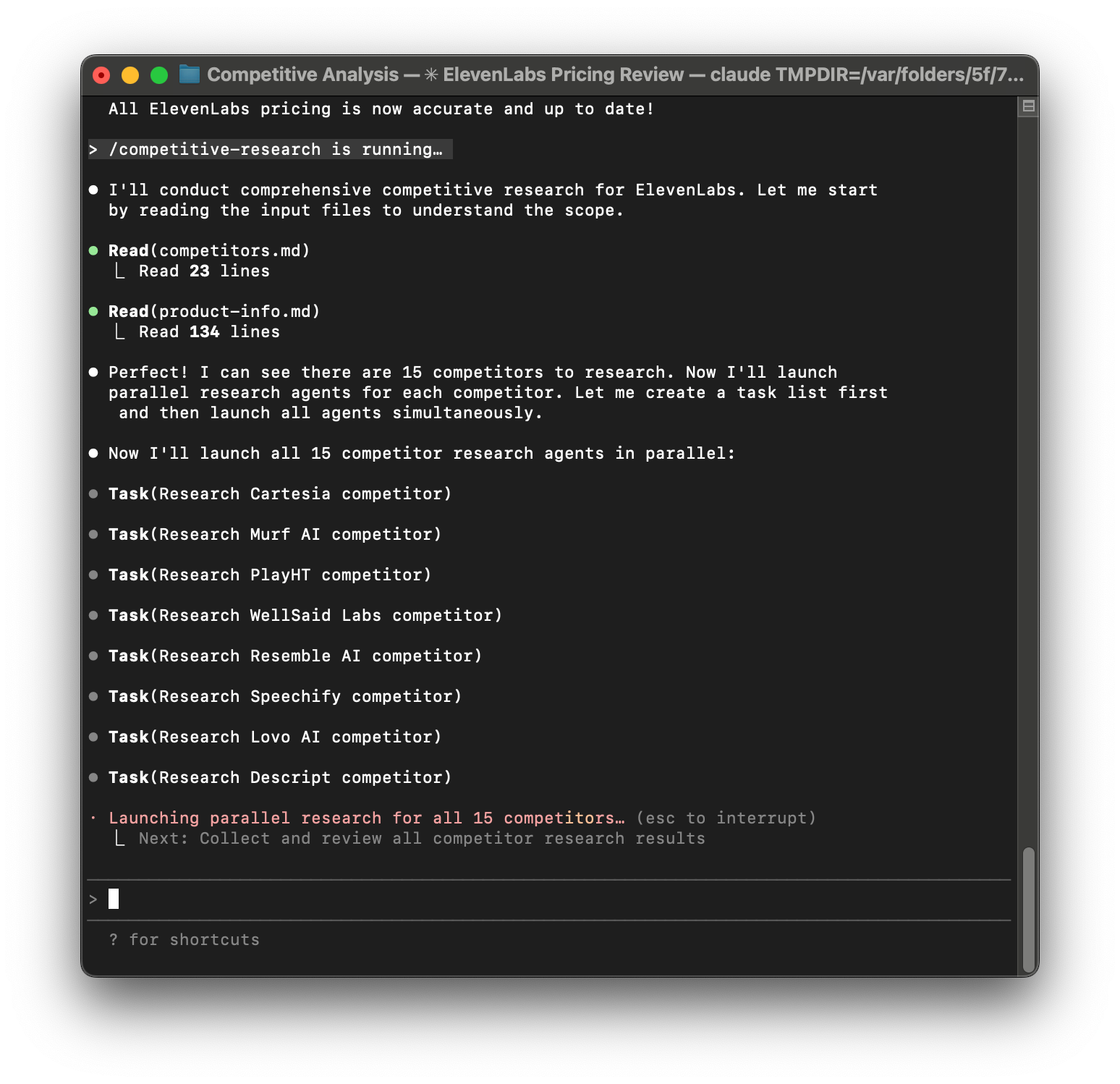
2. Autonomous Code Exploration — Acting as a Junior Security Researcher
Leveraging the agentic capabilities of Opus 4.6, Claude Code Security explores codebases step by step. When it detects suspicious code, it autonomously investigates related files, runs tests with various tools, and traces potential exploitation paths. "It navigates the codebase incrementally, tests how components behave, and follows clues—but at superhuman speed," Graham explains.
3. Self-Verification
After identifying potential vulnerabilities, the system re-evaluates their severity. To minimize false positives, it cross-checks findings and only labels high-confidence, exploitable issues as critical. This ensures security teams can focus on real threats instead of sifting through noise.
4. Fix Suggestions — But No Automatic Patching
Claude Code Security suggests secure code fixes but never applies them automatically. This is an intentional design choice: security patches can affect functionality and must be reviewed and approved by human developers. The model supports with intelligence; humans retain control over implementation.
5. Data Flow Tracing
It maps how user inputs travel through the system. Vulnerabilities like SQL injection, XSS, and SSRF occur when unvalidated data reaches sensitive functions. By tracing the full path from entry point to execution, Claude Code Security identifies exactly where and how the system becomes exposed.
Frontier Red Team — One Year of Internal Research
Claude Code Security wasn’t built overnight. Anthropic’s Frontier Red Team, a specialized internal group of about 15 researchers, spent over a year stress-testing AI models in real-world cybersecurity scenarios. Their findings were startling.
When tested on open-source software running in enterprise systems and critical infrastructure, Opus 4.6 successfully uncovered high-risk Zero-Day vulnerabilities that had remained undetected for decades—all without custom scaffolding, specialized tools, or engineered prompts.
"We're now using [Opus 4.6] in ways that are meaningfully impactful, after extensive experimentation. The model has meaningfully improved—especially in autonomy." — Logan Graham, Frontier Red Team Lead
Availability — Limited Research Preview
Claude Code Security is not yet publicly available. In a cautious rollout, Anthropic is currently offering access only to:
- Enterprise and Team customers: Eligible for limited research preview access
- Open-source repository maintainers: Free and fast access (aimed at supporting under-resourced open-source developers)
This controlled release allows Anthropic to gather comprehensive feedback and minimize potential misuse. While designed as a defensive tool, Anthropic openly acknowledges the same technology could be misused for offensive purposes.
Comparison with Traditional Security Tools
| Feature | Traditional SAST Tools | Claude Code Security |
|---|---|---|
| Analysis Scope | Individual files/functions | Entire codebase |
| Vulnerability Types | Known patterns | Known + new Zero-Days |
| Cross-Component Analysis | Limited | Full support |
| Self-Verification | None | Yes (reduces false positives) |
| Fix Recommendations | Partial | Detailed suggestions (no auto-apply) |
| Data Flow Tracing | Limited | Full-path tracing |
| Autonomous Exploration | None | Agentic navigation |
Impact on Security Teams
Claude Code Security is not designed to replace security engineers—it empowers them. It enables a single engineer to analyze vastly more code, with greater depth and precision. Most enterprise security teams are drastically understaffed relative to the code they must protect. This tool bridges the gap with AI augmentation.
The impact on the open-source ecosystem could be particularly transformative. Much of the world’s digital infrastructure relies on open-source software maintained by a handful of volunteer developers. Anthropic’s decision to offer free access to these maintainers could significantly strengthen supply chain security and prevent widespread exploits.
Caution — A Double-Edged Sword
As Anthropic itself admits, an AI that autonomously discovers vulnerabilities can be a powerful offensive weapon as well as a defensive one. This is precisely why the company is withholding open distribution and opting for a restricted research preview. Anthropic has committed to ongoing monitoring to ensure the model’s capabilities remain focused on defensive, ethical use cases.
Summary — Key Takeaways on Claude Code Security
- Launch Date: February 20, 2026 (Limited Research Preview)
- Base Model: Claude Opus 4.6
- Core Function: Autonomous, full-codebase vulnerability detection
- Key Advantages: Zero-Day discovery, cross-component analysis, self-verification
- Target Users: Enterprise/Team customers, open-source maintainers
- Auto-Fixing: None (only suggestions, human approval required)
댓글
댓글 쓰기